
Report a Stolen Car - International Database - Stolen Vehicles, Bikes, Cars, Trucks, Boats - YouTube

Two million stolen passwords to Facebook and Google posted online: security firm – New York Daily News

Misconfigured database operated by hackers found exposing almost 5GB of stolen credentials | Cyware Alerts - Hacker News

New Irish website aims to stop people from unknowingly buying stolen goods by creating database of robbed property | The Irish Sun

Hackers compile database of people of Jewish descent using stolen 23andMe user data - Washington Times
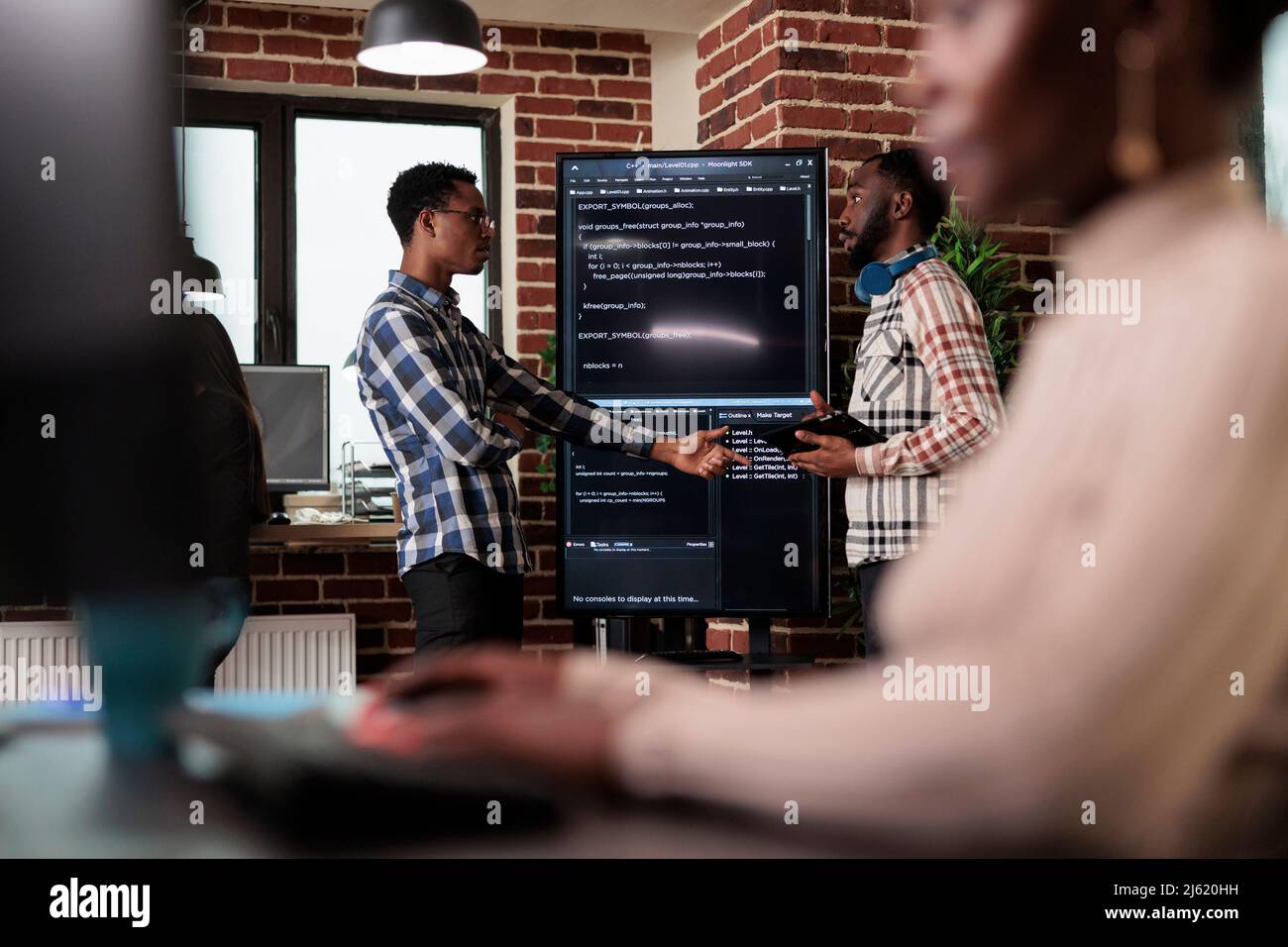
African american software developer pointing out cloud database processing algorithm error. Cybernetics engineers talking about deciphering stolen corrupted and ecrypted important company files Stock Photo - Alamy



















:max_bytes(150000):strip_icc()/identitytheft.asp-final-7eb6d3e2b3434994bcb40226957e3b3c.jpg)

